A hacker has found a backdoor to wireless combination router/DSL modems that could allow an attacker to reset the router’s configuration and gain access to the administrative control panel. The attack, confirmed to work on several Linksys and Netgear DSL modems, exploits an open port accessible over the wireless local network.
The backdoor requires that the attacker be on the local network, so this isn’t something that could be used to remotely attack DSL users. However, it could be used to commandeer a wireless access point and allow an attacker to get unfettered access to local network resources. Update: Vanderbeken reports some routers have the backdoor open to the Internet side as well, leaving them vulnerable to remote attack.
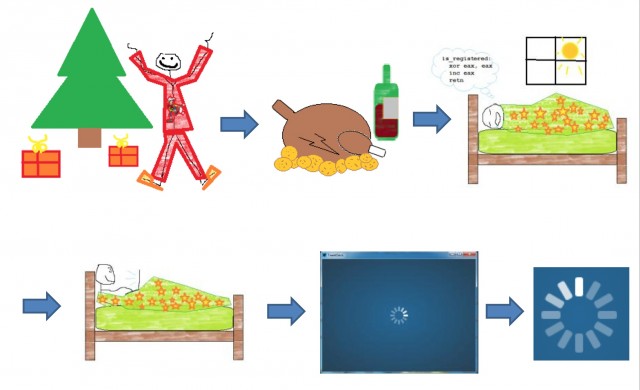
Eloi Vanderbeken described the backdoor in a PowerPoint posted with the code to Github. In his illustrated report, he explained how over the Christmas holiday he was trying to get access to the administrative console of his family’s Linksys WAG200G wireless DSL gateway wirelessly—mostly so he could limit how much bandwidth the others in the house were using. But Vanderbeken had previously turned off wireless access to the administration web console (and had forgotten his administrative password).
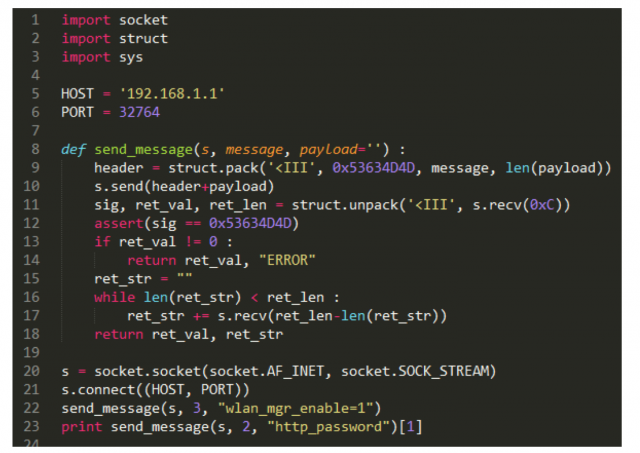
Performing a scan, he found that the router responded to messages over an unusual TCP port number: 32764. A search of the web found other Linksys and Netgear router owers had found the same service, but there was no documentation for what it did.
So Vanderbeken downloaded a copy of the Linksys firmware and commenced reverse-engineering the binary MIPS code. What he found was a simple interface that allowed him to send commands to the router without being authenticated as the administrator. On his first attempt to brute-force the interface, the router flipped its configuration back to factory settings, causing his family members to all lose Internet access at the same time.
After some additional testing, Vanderbecken found that the interface allowed him to execute a number of commands directly against the router, including a command-line shell. Using the commands he discovered, he was able to write a script that allowed him to turn wireless access to administration on and reset the web password, and published the script (with his cartoon report on the backdoor) to Github.
Soon, confirmations that the backdoor worked with other models of Linksys and Netgear wireless DSL modems came flooding in. A commenter on Hacker News noted that the backdoor might affect wireless routers with DSL modems from SerComm, which manufactured many of Linksys’ older DSL modems. A list of SerComm devices from various vendors matches up with the router-modems reported as vulnerable thus far.
reader comments
107