Apple Releases Java Update to Remove Flashback Malware
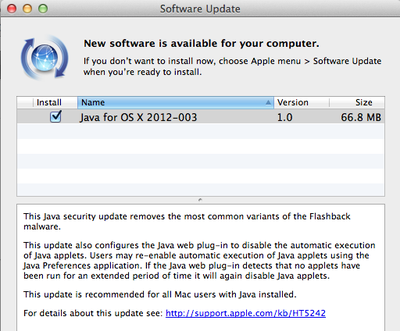
Apple just released Java for OS X 2012-003, an update to the Java implementation in OS X. The update removes "the most common variants of the Flashback malware." Interestingly the update disables the automatic execution of Java applets, and, if automatic execution is re-enabled, will again disable it if no applets have been run for "an extended period of time".
It was reported earlier this week that Apple was in the process of creating software to remove Flashback. It's been claimed that the Flashback malware infected more than 600,000 Macs at its peak, though there have been a number of programs created to quickly and easily cleanse infected machines.
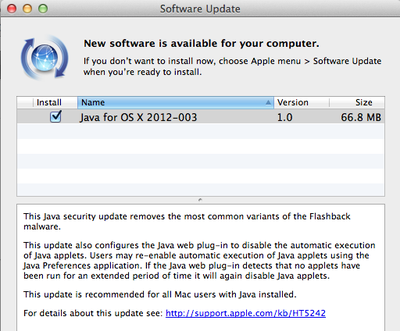
This Java security update removes the most common variants of the Flashback malware.
This update also configures the Java web plug-in to disable the automatic execution of Java applets. Users may re-enable automatic execution of Java applets using the Java Preferences application. If the Java web plug-in detects that no applets have been run for an extended period of time it will again disable Java applets.
This update is recommended for all Mac users with Java installed.
For details about this update see: http://support.apple.com/kb/HT5242
The update can be downloaded via Software Update. A separate Java for Mac OS X 10.6 Update 8 is available for users on Mac OS X Snow Leopard.
Popular Stories
Game emulator apps have come and gone since Apple announced App Store support for them on April 5, but now popular game emulator Delta from developer Riley Testut is available for download. Testut is known as the developer behind GBA4iOS, an open-source emulator that was available for a brief time more than a decade ago. GBA4iOS led to Delta, an emulator that has been available outside of...
Last September, Apple's iPhone 15 Pro models debuted with a new customizable Action button, offering faster access to a handful of functions, as well as the ability to assign Shortcuts. Apple is poised to include the feature on all upcoming iPhone 16 models, so we asked iPhone 15 Pro users what their experience has been with the additional button so far. The Action button replaces the switch ...
The lead developer of the multi-emulator app Provenance has told iMore that his team is working towards releasing the app on the App Store, but he did not provide a timeframe. Provenance is a frontend for many existing emulators, and it would allow iPhone and Apple TV users to emulate games released for a wide variety of classic game consoles, including the original PlayStation, GameCube, Wii,...
A decade ago, developer Riley Testut released the GBA4iOS emulator for iOS, and since it was against the rules at the time, Apple put a stop to downloads. Emulators have been a violation of the App Store rules for years, but that changed on April 5 when Apple suddenly reversed course and said that it was allowing retro game emulators on the App Store. Subscribe to the MacRumors YouTube channel ...
The first approved Nintendo Entertainment System (NES) emulator for the iPhone and iPad was made available on the App Store today following Apple's rule change. The emulator is called Bimmy, and it was developed by Tom Salvo. On the App Store, Bimmy is described as a tool for testing and playing public domain/"homebrew" games created for the NES, but the app allows you to load ROMs for any...


















Top Rated Comments
You're the exact type of user this update was released for.
This isn't a virus. And it's estimated that less than one percent of macs that had the trojan. The OS was in no way affected, it relates to third party software which is being dropped by Apple.
You can't honestly be stupid enough to not know the difference between a Trojan horse and a virus.
Is Flashback a virus? It's malware, but is it a self-propagating virus? And it's not true that Macs have fewer viruses because Windows is "more popular". OS X is inherently more secure, but as Flashback proves, it's not 100% bulletproof. But as Apple has proven with this update, the good design of OS X allows them to protect users, even after an incident arises.